It started simply enough...
Innocuous Beginnings
Our local small-town ski shop posted on their socials the other day, "We have recently found a fraudulent duplicate online web store. Please be sure you are using our correct web address. If you purchased something from the fraudulent site please contact your credit card company immediately."
I was curious, so called them the next day. At least one of their customers had attempted to make a purchase though the site, with no goods being delivered. They didn't know what to do about the situation, so I offered to take a look and got the fake site URL, which was the same as their legitimate site but had a hyphen between two words.
According to whois, the domain registrar was Name.com and the technical contact was in China. DNS services and webfront were Cloudflare. The fake store was using a copy of the real store's logo, had the same product listings (some with unrealistic discounts applied), and even some of the same <head><meta> tags. The fake store's SEO was pretty good, and a lot of their pages were Google indexed.
I drafted up a DMCA takedown notice (redacted template), sent it off to Name.com via their abuse report form, and within 12 hours they'd put the domain into "client hold" status, essentially disabling the domain. Within 24 hours, cached DNS records were mostly timed out and the fraudulent site was no longer accessible. I also put in a removal request with Google, and the content aged out of their indexes pretty quickly.
It only really took about 30 minutes work (and, perhaps, 20 years of accrued knowledge of how the internet works and how abuse is reported / handled).
Done? (meta: how does your average retailer who doesn't have a friendly security person reading their socials deal with this situation?)
Upon Further Investigation
Talking with a co-worker, he security-nerd-sniped me by being curious about what the site content was like & if there were any unique characteristics that could be used to track down other instances. Looking at some of the page content that I'd saved, I noticed that one component in particular was misspelled, likely in a unique way.
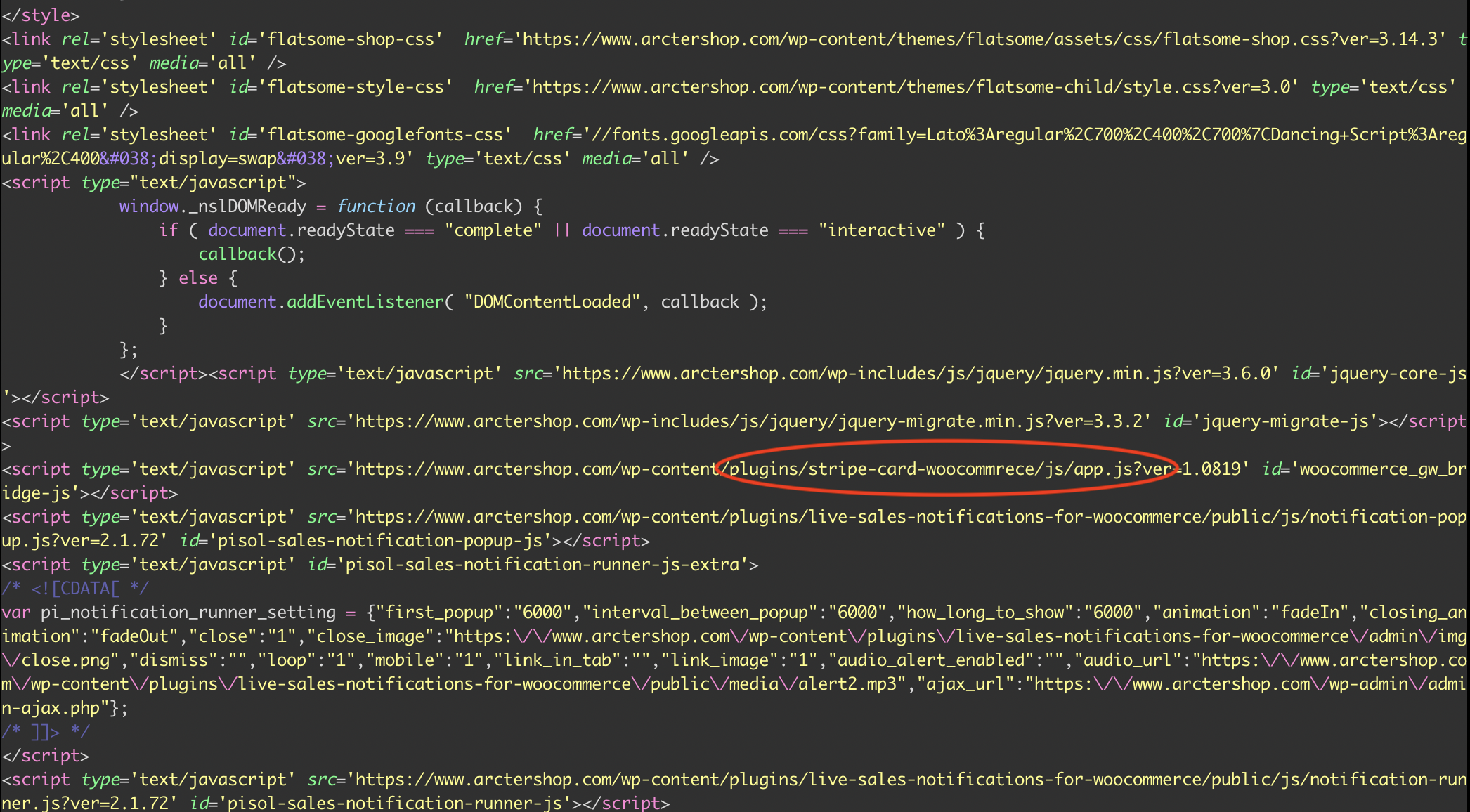
A Google search for stripe-card-woocommrece found two urlscan.io entries for similar-looking sites. Using urlscan.io (specifically, https://urlscan.io/search/#filename%3A%22%2Fwp-content%2Fplugins%2Fstripe-card-woocommrece%2Fjs%2Fapp.js%22's associated API query), I was able to pull out a list of 320 unique sites that has this same misspelled component in them.
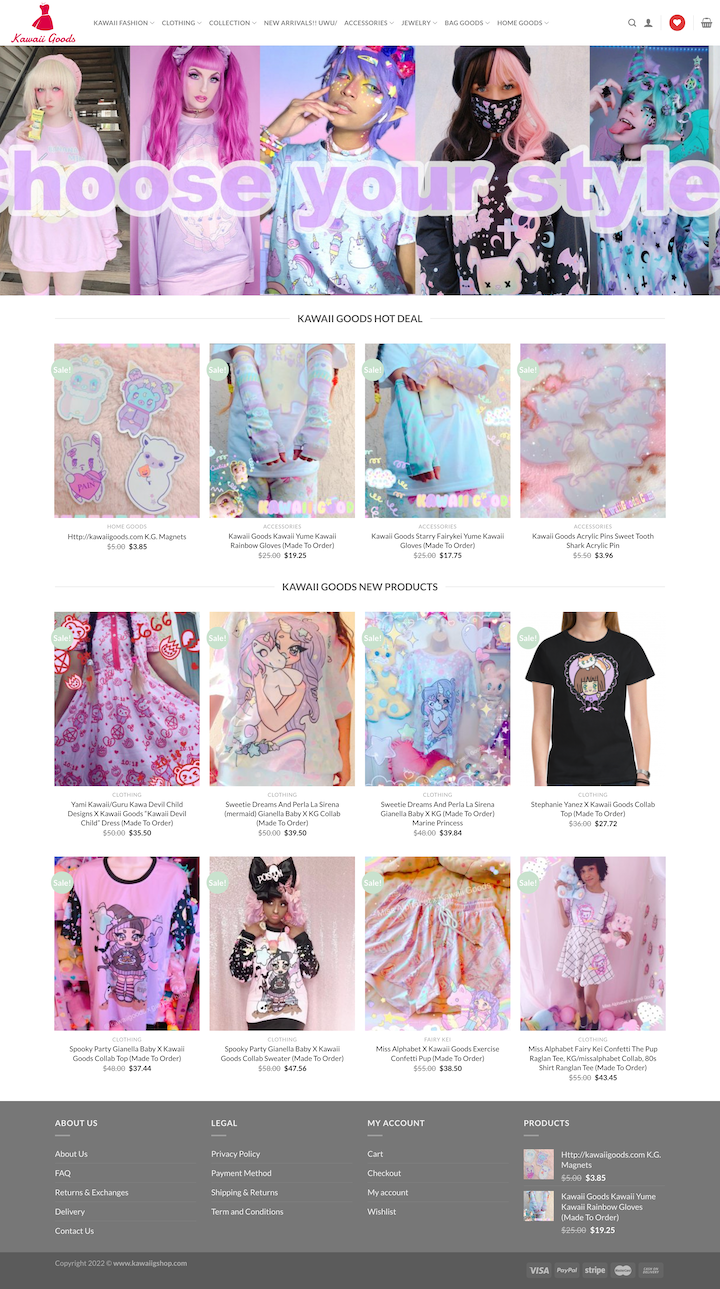
I haven't checked them all, but I've checked a reasonably-sized sample. It's a combination of generic and copycat sites, all laid out in the same fashion, and all reflecting the patterns identified in the first case. It's generally a domain name registered at Name.com (sometimes different for non-.com domains), whois record with a China-based technical contact, with DNS & webfront at Cloudfront, backed by WooCommerce/WordPress, and that typo'd stripe-card-woocommrece in their index.html.
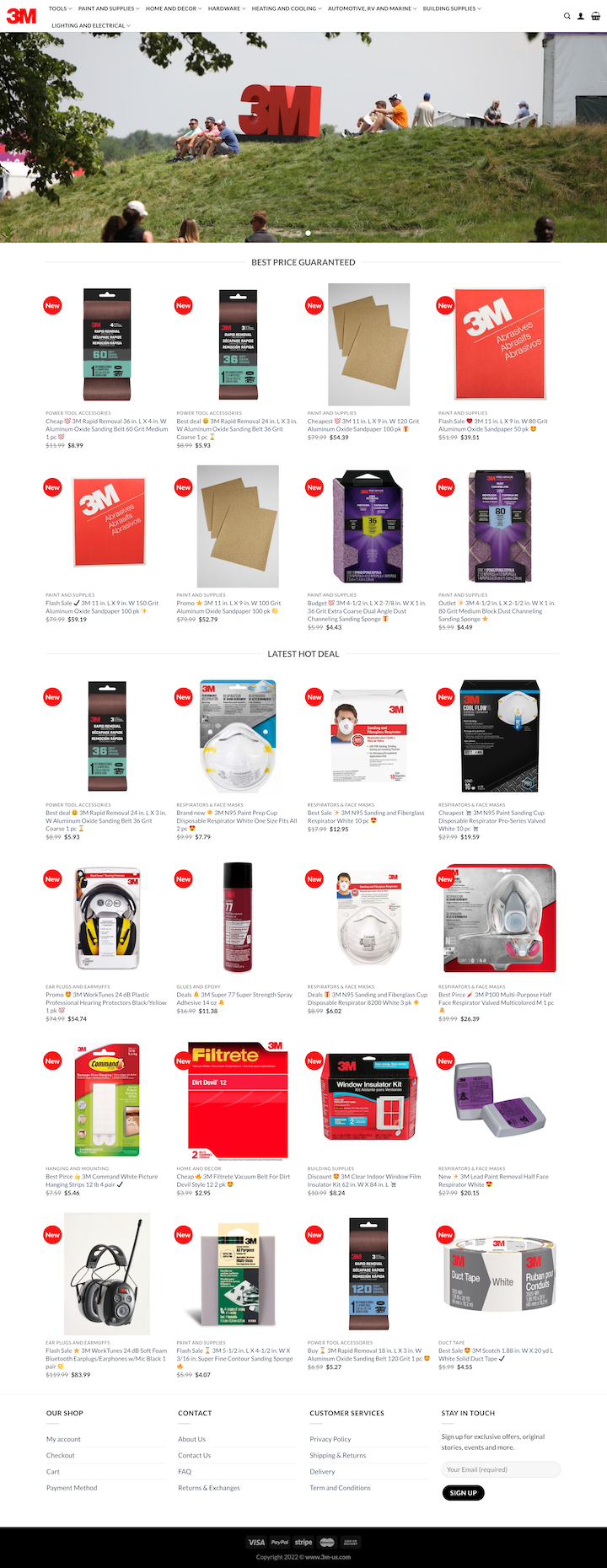
The copycat sites had copied logos and product listings. There was a very similar page layout & footer across all the sites. Some have been translated into different languages.
The search also took me to https://themesinfo.com/wordpress-plugins/wordpress-stripe-card-woocommrece-plugin-eyjh. This is a purpose-built Wordpress crawler that catalogs plugins across Wordpress instances, and tells me that stripe-card-woocommrece WordPress plugin is used on 235 websites.
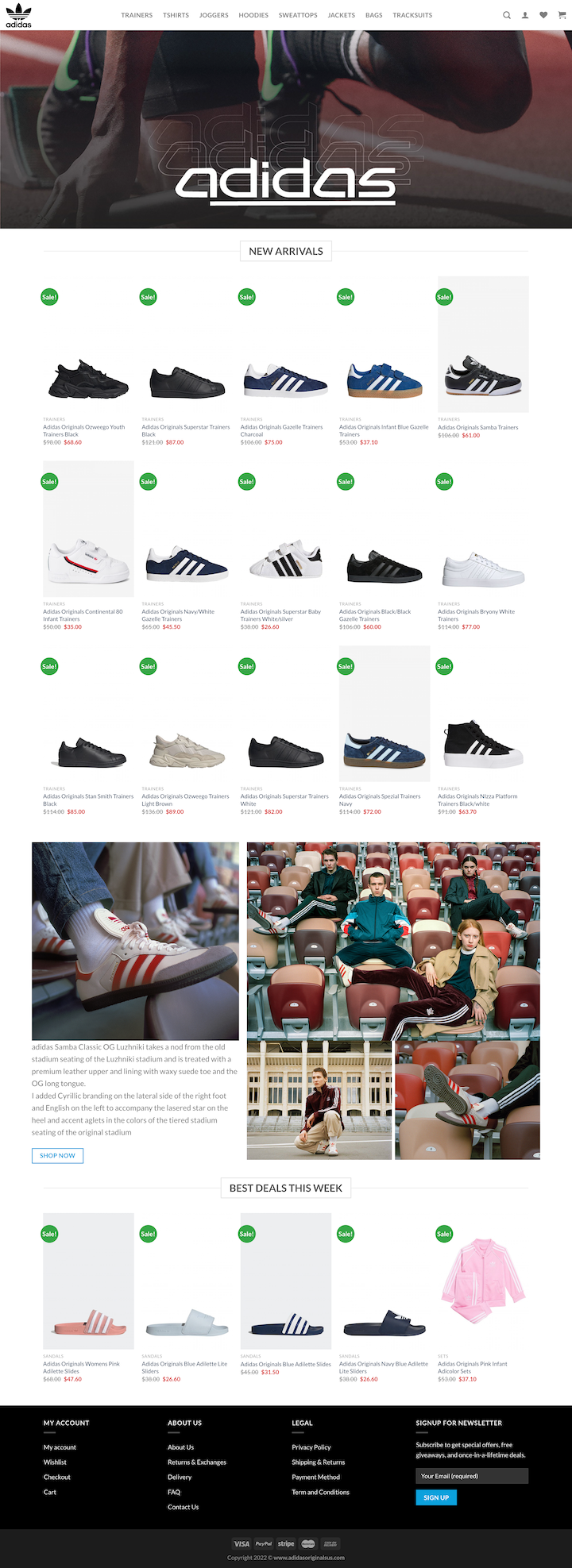
I couldn't be bothered figuring out how to scrape the full list of domains out of this site, but from a manual check there seemed to be some unique items on both lists (https://www.adidasoriginalsus.com/ was a particularly good one from this list).
Neither GitHub nor GitLab have that stripe-card-woocommrece string indexed, so looks like we're not going to get lucky and find a public repository with this code in it.
Done?
Follow The Money
Another co-worker was curious (stop being curious and causing more work for me, co-workers!) about if and / or how these payments were being processed.
The shopping cart / checkout screens and payment forms on these sites feel reasonably well done and don't have any crazy red flags. They generally offer Mastercard, Visa, and Paypal payment methods.
Looking at one of the fake storefronts, https://www.3m-us.com:
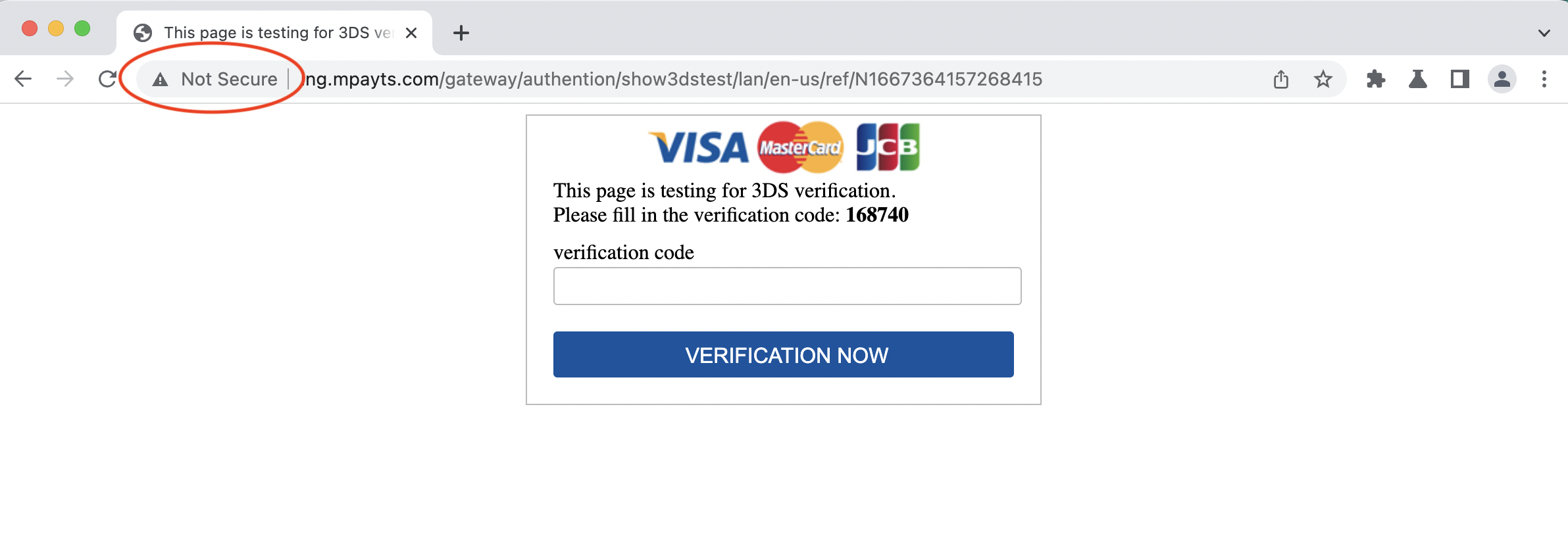
- Doing a Visa payment with a test card # (good ol' 4242 4242 4242 4242) redirects to
ing.mpayts.com/gateway/authention/show3dstest/lan/en-us/ref/N1667359025690114prompting for re-entry of a verification code rendered on the same page (oops, no padlock.. I guess they aren't "protected by 256-bit SSL technology" after all), which then redirects back to the storefront viahttps://www.loreencatalog.site/payment/return.php?code=mpayts&ordersn=66221102111704325. (I suspect they may not be processing payments, but are perhaps collecting credit card details on the backend?)
- Choosing Paypal does result in a redirect to
https://www.paypal.com/cgi-bin/webscrand what looks like a legit login form, viawww.antasas.com/check_purchase/shop_payment_handle.php. The Paypal page has a 'Cancel and return to Todd Le' link at the bottom, pointing back tohttps://www.antasas.com/check_purchase/pay_info_for_cancel.phpwhich then redirected throughxilapay.nettopsyupay.com(similar-but-different fake storefront).
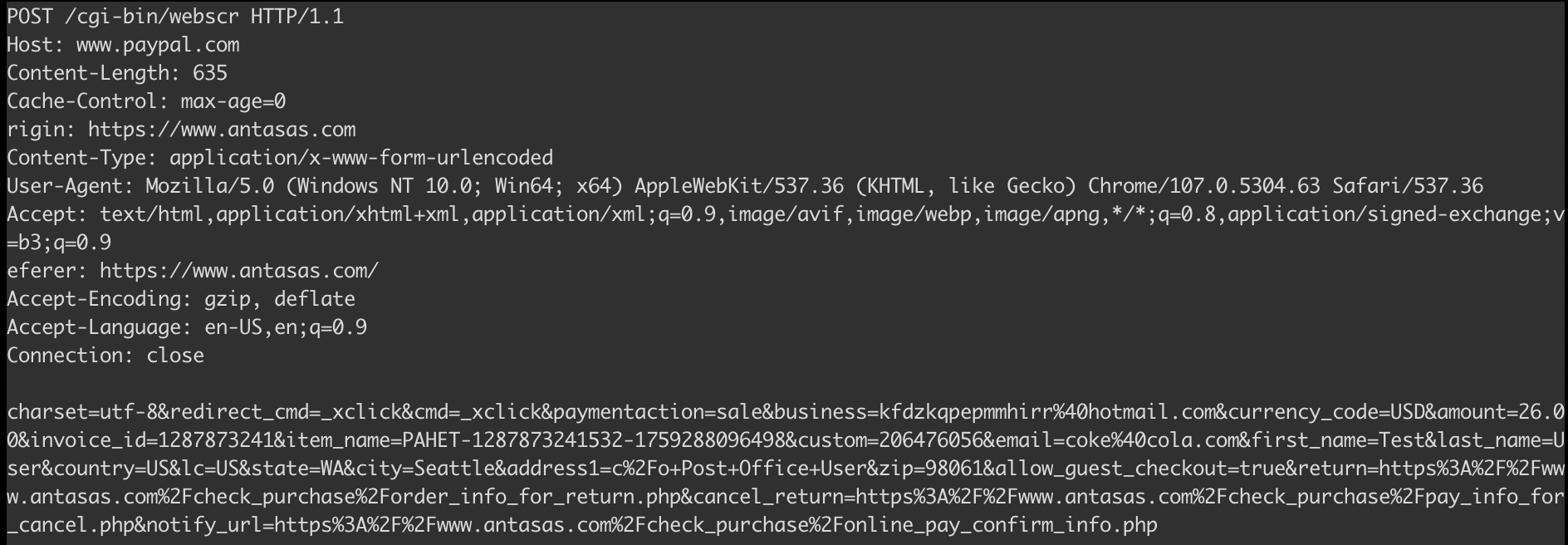
Looking at a second fake store front, https://www.converseofficial.com/, we see the same deal. A Visa payment with test card redirects through ing.mpayts.com then www.loreencatalog.site before landing back at the fake storefront. Paypal behavior is the same, with the same 'Todd Le' cancellation link (perhaps there's a shared Paypal merchant account under the hood here?).
What Next?
I'm not quite sure but somehow helping out the local small-town ski shop has lead to this. Perhaps all these sites are legit but.. I don't think so. Is this level of probably-fraud just situation-normal for the internet these days?
Ehh, who knows! Find some way to flag copycats with the individual brands in question? Report en masse to Name.com, Cloudflare, and Paypal abuse/fraud teams? Go straight to the FTC?
Or just hit publish and move on with life.
Done?
The List
(...or partial list, according to https://urlscan.io.)
Some of the sites on this list seem to have been taken down already - perhaps some brands are better at monitoring their domain name space than others?
The uniformity-but-not of these sites is really quite impressive. I'm morbidly curious what their deployment pipeline / management tooling looks like.
3m-us.com
abercrombie-fitch.shop
abercrombiefr.com
abussconto.com
academkstar.com
acclaim-usa.com
acdelco-store.com
agentprovocateurshop.com
aircraft-security.com
alexandersoldes.com
allsafesecurity.shop
alpinestars-it.xyz
annououtlet.com
annoushkashop.com
applepikolinos.com
appletredeals.com
arctershop.com
armaniexchange-fr.com
armanisale.com
asos-soldes.com
asos4505shop.com
atlas-sale.com
autrysstore.com
avalanche-safety.com
avalanchesafety.shop
axels-outpost.com
babebodyarmor.com
bags-containers.com
bally-sale.com
bankside-tackle.com
barbourshop.xyz
beachlifeaustrade.shop
bershkasoldes.com
bestninewest.store
bestseebychloe.com
beststevemadden.shop
bestsuperdry.com
billabongmutual.com
billabongonline.com
billabongsales.com
billabongus.com
billiards-shops.com
billiards-store.shop
billieblushuk.com
billinisale.com
billiniusas.com
billtornadebits.com
blackriflecoffee.shop
blackriflecoffeecompany.shop
blade-us.com
bladediscount.com
boatsmodel.shop
boilsofas.com
boschakkus.com
brokedowns.com
cachecache-es.xyz
cachecache.shop
carlyleavenues.com
chainsawtag.com
cheaopigloo.com
cheapbigapple.com
cheapmaskus.com
cheapoffwhite.xyz
cheapquality.cyou
christopheresbers.com
citybeachoutlet.shop
cks-onlines.com
cldepeaubeaut.shop
cleachocfy.com
climatescontrol.com
containersski.com
controlski.com
controlstrap.com
converseofficial.com
coreididentity.de
covedecorate.com
covenantsecurity.shop
croc-soldes.com
datatsecurity.com
deltachildren.shop
dhpstore.com
diamond-sport-gear.com
dimmbarlamb.com
diningfurniture-shop.com
discordsoldes.com
discount-mac.com
discountigloo.shop
dolce-gabbanafr.com
doorswindowsli.com
dunelondons.com
eastsidemus.com
einhellverkauf.de
elkmontshop.com
eternaneu.de
evenoddes.com
f1-authentics.shop
f1authentics.shop
facemaskzoot.com
familyoutdoorplayactivity.com
flyfishngonline.com
formal-dresss.com
formasconto.shop
foxracestore.com
french-kitchen.com
friboomagasin.com
frilufgebote.de
gabfacemask.com
garminshops.com
geeks-outpost.com
glovegear.shop
goggles-it.com
gogglesofficial.com
greatrexpromo.com
greengates.shop
grundyshoes.com
hachimanshop.space
hair-beautymart.com
hawkendiscount.com
helmidfr.com
hilldalestore.com
homedecormores.fun
hon-store.com
hunkemollerfr.com
hunkemolleritalia.xyz
hunkemolleruk.com
hunterfanus.xyz
hunteroriginal.shop
huntersski.com
husqvaoutlet.com
ikeasfurniture.com
intentionally-us.com
jacketszape.com
jcrewofficial.com
juicycouturestore.com
justcavallis.com
karlkanivendita.shop
karllagerfeldshop.com
karllagfr.com
keenverkauf.de
kinto-store.com
kleintools-us.com
knix-store.com
kobalt-store.com
kobaltusa.com
kongesslojdzzoo.com
konglaptop.com
kotonit.shop
lacostede.xyz
landdiscount.xyz
laurenralphit.xyz
lavinia-lingeries.com
lc-waikiki.xyz
leattvendita.com
legorestore.com
leslampesgolf.com
levis-official.com
levis-rebaja.com
levisbeach.shop
lexus-shop.com
livestocks-shop.com
lorenzsconto.shop
luisaverkauf.cyou
machina-us.shop
makitaus-shop.com
marceloburlon.de
marceloburlons.xyz
marksspencer.xyz
marksspencershop.com
marshallshop.xyz
marshlandus.com
matchhomeware.com
maxfli-sales.com
merchandise-us.com
michaelcostellos.com
miharayasuhiroshop.com
milediscount.com
milwaukeechan.com
mimilula.shop
mineralmikes.com
missguideds.com
morgansconto.online
musicvideobest.com
new-carvela.com
new-debeers.com
new-safety-us.com
newbaseballgear.com
newbluebuffalo.com
newcanadagoose.xyz
newdisneystore.com
newlanvin.com
newmarcjacobs.xyz
newmoenfaucet.shop
newmotocentral.com
newpinko.com
newstevemadden.com
newteam-rhino.com
northface-us.com
nydjoutlet.com
only-sons.com
oreinternational.space
ospreydiscount.com
outdoor-power.com
oyshosoldes.com
packagedealsale.com
paigeoutlet.com
patagonia-us.com
patriotlighting.shop
paulmith.com
paulsmith-sale.com
paulsmithstore.shop
pieronesoldes.com
pinko-soldes.com
pinkoniedrig.cyou
posteasouderfr.com
postmortemsale.com
postpumps.com
prada-prada.shop
pspaulsmith.shop
radleystores.com
rapido-sales.com
rapidostores.com
rayban-stores.com
redberryapples.com
redefined-rebel.xyz
redefinedrebel.xyz
remeubles.com
retrofeteshop.com
robbies-billiards.shop
rollerskate-us.com
safeers.com
safety-sale.com
safetybootsgle.com
safetyboutique.shop
safetycansnight.com
safetyfootwearonline.com
safetypromo.shop
saintlaurentn.store
saintlaurentshop.com
salomons-shop.com
salsabasprix.com
salvatoreferragamo.xyz
sawbladefiber.com
scieabois.com
seafollyaustralia.com
shoplifestyleshop.com
sicherheitde.com
skateboardssale.xyz
snowboardracks.shop
sorelshop.com
south-beach.xyz
southwireshop.com
sportubeshop.com
spruhpistole.com
starlighshop.com
stell-mccartney.com
steve-handbags.xyz
stevemadden-sale.com
stevemaddenit.xyz
stevemaddenpascher.com
stevemaddensale.com
stevemaddenstore.com
stevemaddenwomen.shop
stuhleclient.com
sunseeker-au.com
superdry-studios.com
superdryenfr.xyz
superdryx-store.com
supportjeans.com
swarovskifr.shop
tail-sales.com
tasakishop.com
tatamifightwears.com
terrycostasale.com
testingster.com
testors-sales.com
the-revit.shop
the-superdryshoes.com
thefornasetti.com
thegirlswithgem.com
thejadedlondon.com
themenlevis.com
thenorthfaces.xyz
theoffbroashop.com
thepatagonias.com
thepinko.xyz
thepocoutlet.com
thercboats.shop
theslazengers.com
threadbareshop.xyz
ticketbattery.com
tiscous-shop.com
topshopblue.com
trackfield.shop
trackfieldsale.com
trackfishing.com
trackspants.com
trouser-sale.com
trouser-store.com
tumisale.com
ufcsshop.com
underarmourtex.com
undersarmours.com
unif-outlet.com
us-shorestore.com
usbedsonlegs.com
vanquish-rccars.com
vans-sale.com
versacecouture.shop
versacecouture.store
versaces.xyz
vivomasksstore.com
vuori-store.com
widefit-shoes.com
wolford-it.xyz
womens-jdy.xyz
yukilamppost.com
zcravestore.com
zegnasales.com
zenonesportsde.de